Anúncios
Strengthening Your App Security Toolkit from the Start
Identifying the Two Factors in Everyday Use
Anticipating Common App Prompts and Phrases
| Authentication Method | User Convenience | Security Level | Best Use Scenario |
|---|---|---|---|
| SMS Code | Easy | Medium | General accounts where speed matters more than absolute safety |
| Authenticator App | Moderate | High | Banking or social media apps needing stronger defense against attacks |
| Email Link | Easy | Medium | Work accounts or collaboration tools with frequent email access |
| Biometrics (Face/Touch) | Very Easy | High | Phones with secure sensors, for those who dislike typing codes |
| Physical Security Key | Challenging | Very High | Developers, administrators, and anyone guarding critical app data |
Pinpointing the Best Method for Your Needs
Factoring in Your Daily App Habits
- Choose app or push-based two factor authentication mobile for international travel — texts may not always come through reliably.
- Set up backup codes and print or write them down. Store securely if you ever lose your device or change your phone number.
- Activate biometric authentication for repeated, private access — it’s quicker and less prone to interception than codes sent over the internet.
- Review each app’s security settings yearly. New methods for two factor authentication mobile may appear and sometimes provide smoother logins or greater safety.
- Don’t use email-only verification where you share email access or devices; anyone nearby could intercept your login process and gain entry.
Assessing When to Change Your Method
- Update backup phone numbers as soon as your main line changes. Recovery will be impossible if two factor authentication mobile relies only on lost contacts.
- Change or reset security questions anytime someone else might know your answers. Unpredictable questions mean stronger two factor authentication mobile defense.
- Rotate which authentication app you use if features or interfaces become unintuitive. Quick access boosts your willingness to stick with two factor authentication mobile every time.
- Consider switching to a physical security key if travel or work demands the absolute best defense—especially against phishing or targeted attacks on two factor authentication mobile.
- Regularly test your recovery methods by signing out and back in, to confirm your backup two factor authentication mobile steps are ready for emergencies or device loss.
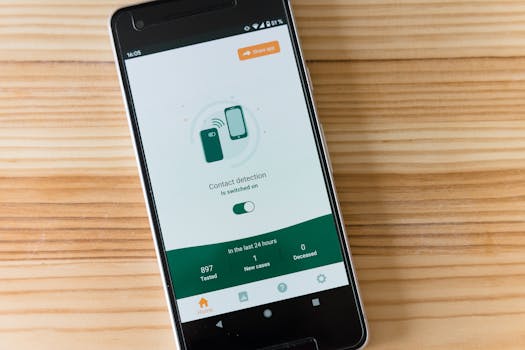
Executing Step-By-Step Enrollments in Major Apps
Switching Between Mobile and Desktop Setup Paths
Enabling Recovery Codes and What to Watch For
Reacting to Everyday Security Signals During Login
Navigating Suspicious Activity Notifications
Taking Preventive Action After a Security Alert
Adapting Two Factor Authentication to Your Changing Needs
Integrating Family Members or Colleagues
Managing Multiple Accounts or Devices
Maintaining Your Security Beyond App Updates